New Release: Tor Browser 14.0

Tor Browser 14.0 is now available from the Tor Browser download page and our distribution directory. This is our first stable release based on Firefox ESR 128, incorporating a year's worth of changes shipped upstream in Firefox. As part of this process we've also completed our annual ESR transition audit, where we reviewed and addressed over 200 Bugzilla issues for changes in Firefox that may negatively affect the privacy and security of Tor Browser users. Our final reports from this audit are now available in the tor-browser-spec repository on our Gitlab instance.
Firefox's design also continues to evolve, and the ESR transition is our opportunity to update Tor Browser to reflect the most recent patterns and styles used in Firefox. For example, eagle-eyed Tor Browser users will notice updates to Tor Browser's typography that we've inherited from Firefox, including heavier headings and changes to line heights intended to improve font compatibility and accessibility.
In addition to the ESR, we overcame many other technical challenges that you can read more about in Morgan's series of blog posts chronicling the team's progress with Tor Browser Alpha, including: unifying Tor Browser for Android's codebase into a monorepo, addressing reproducibility issues in our Android APK generation, reducing Android's APK size for x86 and x86_64 platforms, and changes to how we spoof Tor Browser's user agent, to name a few. This release also includes a series of improvements to the usability and compatibility of our fingerprinting protections without compromising their effectiveness, allowing us to enable useful features like picture-in-picture, screenshots and more.
The ongoing development of Tor Browser is made possible thanks to the support of our community. If Tor Browser is important to you, now is a great time to support our mission, as all donations will be matched through the end of the year.
What's new?
New circuit for Android
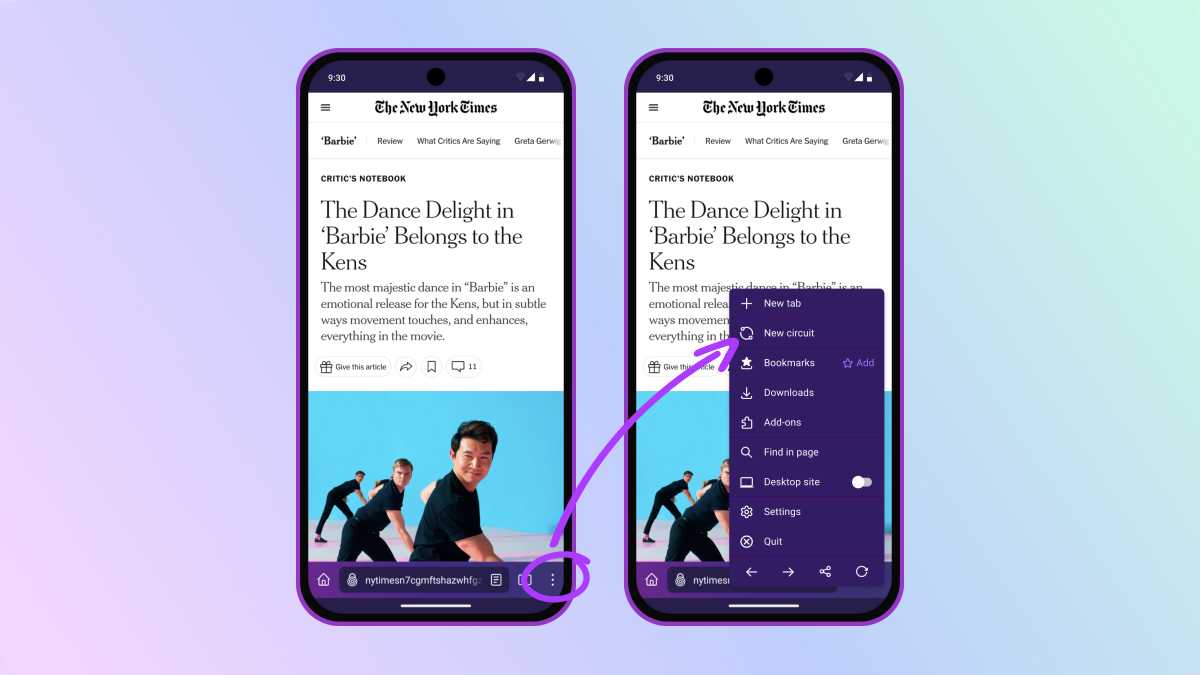
In previous versions of Tor Browser for Android, users could request a "New identity" by interacting with a persistent notification that appeared while Tor Browser was running. However this was unusual for a couple of reasons – firstly, no such feature was available in the app's user interface itself, and it could only be enabled outside the app via Android's notification drawer. Secondly, this feature did not perform the same steps as Tor Browser for desktop to reset your identity, such as closing all tabs, clearing all cookies and wiping your browsing history. In actuality, it functioned more like a "refresh all circuits" button.
We've since learned that most Android users were relying on this feature as workaround to request a new circuit for a broken website, rather than reset their identity as such. So when this notification inadvertently disappeared in Tor Browser 13.5, we didn't rush to bring it back in its original state. Instead, we chose to focus our efforts on porting the desktop feature "New circuit for this site" to Android, allowing our mobile users to request a new circuit in a more targeted fashion.
Extended support for legacy platforms
With the release of Tor Browser 13.5, we began warning users of Windows 7, 8 and 8.1 and macOS 10.12, 10.13 and 10.14 that this would be the last major release to support their platforms. In short, that situation has now changed, and users of these legacy platforms will continue to receive critical security updates updates on a temporary basis until at least March 2025.
Microsoft ended support for Windows 7, 8 and 8.1 in January of 2023, and Apple typically provides support for the previous three versions of macOS. In turn, Mozilla moved support for these versions to the Extended Support Release (ESR) of Firefox last year, and ESR 115 will be the final version of Firefox to support these platforms. However, Mozilla have since announced that ESR 115 will continue to receive critical security updates until at least March 2025, with the intention to re-evaluate the situation at the beginning of the year.
So how does this affect Tor Browser users? That's where it gets a little complicated: Tor Browser 13 is currently based on Firefox ESR 115, whereas Tor Browser 14 is based on ESR 128 – which doesn't support these legacy platforms. This means that the Tor Browser user base will be split across two update paths:
- Users of Windows 10 or later and macOS 10.15 or later will be updated to Tor Browser 14.0.
- User of Windows 7, 8 and 8.1 and macOS 10.12, 10.13 and 10.14 will remain on Tor Browser 13.5.
In turn, the Tor Project will continue to release new versions of Tor Browser 13.5 whenever critical security updates are made available for Firefox ESR 115. Ultimately, this support is only temporary, and is dependent on Mozilla's timetable. Therefore we strongly recommend users of legacy Windows and macOS platforms upgrade their operating systems in order to update to Tor Browser 14.0 before the extended support window ends. Keeping Tor Browser up to date is critical to protect your privacy, security and anonymity online.

Known issues
Tor Browser 14.0 comes with a number of known issues that are searchable on Tor Browser's Gitlab project. In particular, Windows and Android users should be aware of the following:
Android
We are currently working on a fix for an issue with Guardian Project's F-Droid repo that's been preventing F-Droid users from updating since Tor Browser 13.5.3's release. Until this issue is resolved, Android users who have installed Tor Browser via Guardian Project's F-Droid repo will not receive the 14.0 update. Google Play is unaffected by this issue, and Tor Browser 14.0 can be downloaded from there in the interim. Alternatively, affected users may download and install the APK for Tor Browser 14.0 directly from our download page, however please note that APKs do not update automatically. For more details, see tor-browser#43208.
Windows
Running Tor Browser in compatibility mode in Windows 10 and 11 can make it appear as though you're using Windows 7 instead. Given the minimum support requirements for Tor Browser 14.0 described above, Windows 10 and 11 users will need to ensure compatibility mode is switched off before they can update to 14.0.
Contributors <3
Thanks to all of the teams across Tor, and the wider community, who contributed to this release. In particular we'd like to extend our gratitude to the following volunteers who have contributed their expertise, labor, and time to this release:
cypherpunks1
Thank you for tackling the (now shrinking) list of Android bugs, UI discrepancies, and packaging problems. The Android release is more polished than it otherwise would be because of your help.
- tor-browser#41550
- tor-browser#43052
- tor-browser#43129
- tor-browser#43146
- tor-browser#43147
- tor-browser#43202
- tor-browser#43223
- tor-browser#43225
- tor-browser#43227
- tor-browser#43228
- tor-browser-build#41261
NoisyCoil
Thank you for bringing us one step closer to reproducible aarch64 Linux builds. This merge-request was long in the making.
thorin
Last but not least, a big thank you to thorin for your help keeping track of and flagging upstream issues, developing tests, verifying our fixes, maximizing Tor Browser's fingerprinting protections, and for being an ever present advocate for user privacy in general.
If you would like to contribute to a future release, please see our guide for new contributors to get started. If you find a bug or have a suggestion for how we could improve this release, we'd love to hear your feedback.
Full changelog
The full changelog since Tor Browser 13.5.7 for desktop and Tor Browser 13.5.8 for Android is:
- All Platforms
- Bug tor-browser#30543: compat: make spoofed orientation reflect spoofed screen dimensions
- Bug tor-browser#30862: 10ms time precision via EXSLT date-time function
- Bug tor-browser#41328: Follow firefox ESMify for Bug 1308512
- Bug tor-browser#42054: ESR128: investigate - thorin's list
- Bug tor-browser#42220: Flip all the possible preferences to prevent any automatic download
- Bug tor-browser#42255: pdfjs.disabled used to be part of RFP until Bug 1838415; lock pref to false in stable
- Bug tor-browser#42356: Review 000-tor-browser.js and 001-base-profile.js for 128
- Bug tor-browser#42601: Check Bug 1894779: Allow font-face urls to be resource:// urls and relax CORS for resource:// URLs
- Bug tor-browser#42611: Set clipboard.imageAsFile.enabled to false
- Bug tor-browser#42646: Drop patch for tor-browser#40166
- Bug tor-browser#42683: Create script to generate issue triage csv's from bugzilla query and git scraping
- Bug tor-browser#42684: Disable network prefetch
- Bug tor-browser#42685: compat: ESR128: enable textmetrics
- Bug tor-browser#42716: Disable unwanted about:* pages
- Bug tor-browser#42730: Make RemoteSettings use only local dumps
- Bug tor-browser#42746: Extend prefers-contrast rules to include forced-colors
- Bug tor-browser#42759: CI: remove localization file names that are in neither 14.0 nor 13.5 branches
- Bug tor-browser#42814: Opt out from Firefox relay by default.
- Bug tor-browser#42830: Enable WebAudio APIs
- Bug tor-browser#42831: Remove the shopping components
- Bug tor-browser#42867: Disable contentRelevancy component
- Bug tor-browser#43011: Ship only one copy of the MIT license, like upstream.
- Bug tor-browser#43012: Mixed content: browser requests HTTPS images from onion domain accessed via HTTP
- Bug tor-browser#43013: security.mixed_content.upgrade_display_content.image is true by default
- Bug tor-browser#43054: check bounceTrackingProtection in PB mode does not persist to disk
- Bug tor-browser#43074: Pass the browser to TorDomainIsolator.newCircuitForBrowser
- Bug tor-browser#43144: Ensure non-privacy browsing also sets the GPC header
- Bug tor-browser#43163: Disable offscreen canvas until verified it is not fingerprintable
- Bug tor-browser#43170: Disable user-agent spoofing in HTTP header
- Bug tor-browser#43178: Audit fingerprinting overrides (MozBug 1834274)
- Bug tor-browser#43184: Backport Bugzilla 1922294: RFP: fixup square spoofed orientation
- Bug tor-browser#43197: Disable automatic exception for HTTPS-First
- Windows + macOS + Linux
- Updated Firefox to 128.3.0esr
- Updated NoScript to 11.4.42
- Bug tor-browser#40147: Re-enable Picture-in-Picture mode
- Bug tor-browser#41309: Re-enable screenshots component
- Bug tor-browser#41811: Primary buttons that result in a connection attempt should be purple
- Bug tor-browser#41817: Add more color aliases that take dark mode into account
- Bug tor-browser#41820: Downloads warning styling improvements (use moz-message-bar)
- Bug tor-browser#42070: Backport Bugzilla 1834307 and hide smooth-scroll UX
- Bug tor-browser#42212: Fluent migration: onion services
- Bug tor-browser#42362: "New window" missing from File menu
- Bug tor-browser#42441: Evaluate RR version-by-RR version rebases instead of ESR-to-ESR
- Bug tor-browser#42488: ESR 128: Remove role="code" from tor circuit panel
- Bug tor-browser#42603: Remove safebrowsing URLs
- Bug tor-browser#42612: Re-implement moz-toggle customizations for ESR 128
- Bug tor-browser#42617: Restore the HTML form on DDG when using safest in 128
- Bug tor-browser#42629: Tweak
isOnNewTabPagepatch - Bug tor-browser#42630: Review LaterRun in 128
- Bug tor-browser#42640: Disable Firefox Flame button due to unknown interactions with New Identity
- Bug tor-browser#42641: Move from panel-footer class to moz-button-group
- Bug tor-browser#42643: downloads panel separator has mismatched margin
- Bug tor-browser#42644: toolbar rules in panelUI-shared.css are unneccessary
- Bug tor-browser#42647: "Switching to a new device" regressed on 128
- Bug tor-browser#42653: The Neterror page has a checkbox to report iframe origin errors to TPO
- Bug tor-browser#42662: Use data-hidden-from-search for hiding the firefox connection settings
- Bug tor-browser#42663: Tor Browser "Connection" settings missing a tooltip
- Bug tor-browser#42665: Drop "Learn More" spacing
- Bug tor-browser#42667: Add description-deemphasized class to our additions to about:preferences
- Bug tor-browser#42679: Use a more robust approach to hide the "tracking protection" urlbar button
- Bug tor-browser#42687: Disable Privacy-Preserving Attribution
- Bug tor-browser#42695: Use
--arrowpanel-variables for tor circuit panel spacing - Bug tor-browser#42698: Bridge card background contrast is low for bridge-moji
- Bug tor-browser#42699: Drop level="top" attribute from panels
- Bug tor-browser#42700: Remove !nodes condition from gTorCircuitPanel._updateCurrentBrowser
- Bug tor-browser#42704: Drop the badged="true" attribute from security level button
- Bug tor-browser#42705: Update our preferences to account for new line height
- Bug tor-browser#42713: Some --in-content CSS variables were renamed/removed
- Bug tor-browser#42718: Remove the firefox-view button from UI, even when always-on private-browsing mode is disabled
- Bug tor-browser#42735: Disable recent search suggestions
- Bug tor-browser#42740: Stop trying to hide "Restore previous session"
- Bug tor-browser#42742: Inconsistent use of "New private window" vs "New window"
- Bug tor-browser#42743: Invalid onion sites are shown as secure in the page info window
- Bug tor-browser#42744: Light theme override for "about:tor" is inherited by chrome error pages.
- Bug tor-browser#42745: Remove some residuals from update scripts
- Bug tor-browser#42764: Unconditionally disable find-bar transition animation
- Bug tor-browser#42777: Remove 'Website Privacy Preferences' and ensure sensible default prefs
- Bug tor-browser#42803: Lost focus styling for built-in bridges radio options
- Bug tor-browser#42806: Use the
lhCSS unit - Bug tor-browser#42872: Disable translations until audited and solved the UX problems
- Bug tor-browser#43015: Missing region-name-skr fluent entry when fetching TorConnect country names
- Bug tor-browser#43067: Use html:link rather than xml-stylesheet in our dialogs
- Bug tor-browser#43071: Make sure "tor-button" elements that are also "primary" still use the tor colors
- Bug tor-browser#43072: moz-message-bar does not get announced on Orca screen-reader
- Bug tor-browser#43075: Should we drop link spacing in about:tor
- Bug tor-browser#43081: Remove hard-coded CSS
line-height - Bug tor-browser#43082: Search engine icon is not shown while typing in the address bar
- Bug tor-browser#43083: Backport fix for Mozilla 1436462
- Bug tor-browser#43087: Onion pattern on about:torconnect needs a dark theme asset
- Bug tor-browser#43103: Verify whether an update is unsupported before choosing one
- Bug tor-browser#43104: Local files and extensions can't be loaded in new windows before bootstrap
- Bug tor-browser#43105: Migrating Disconnect is not needed anymore
- Bug tor-browser#43109: Remove mention of Firefox Relay from settings
- Bug tor-browser#43115: Height of search bar has collapsed on about:tor
- Bug tor-browser#43117: Hide 'Always underline links' option
- Bug tor-browser#43118: hide CFR
- Bug tor-browser#43131: Reduce layout jank when loading about:tor
- Bug tor-browser#43134: Backport Bugzilla 1436226 Hardcode VP8/VP9
- Bug tor-browser#43164: Prevent search-bar from being auto-hidden when not used for awhile
- Bug tor-browser#43169: compat: align userAgent in navigator + HTTP Header
- Bug tor-browser#43174: Issue with custom home page on local filesystem
- Bug tor-browser#43209: UI freezes when clipboard is empty after screen lock
- Bug tor-browser#43217: Fullscreen videos have rounded letterboxing corners
- Bug tor-browser#43218: Switch to browser.reload, since Browser:Reload signal was dropped upstream
- Bug tor-browser-build#41248: Check and update bundled font versions
- Windows + macOS
- Bug tor-browser#43021: Revert the OS deprecation notification introduced in #42347
- macOS + Linux
- Bug tor-browser#42467: Make OS HTTP User-Agent OS spoofing configurable by pref
- Windows
- Bug tor-browser#43051: windows: remove UI for "open Tor Browser automatically when computer starts"
- macOS
- Bug tor-browser#42494: mac: add Arial Black and Arial Narrow to allowlist
- Linux
- Bug tor-browser#42702: Cannot access the clipboard for the crypto address check (wayland)
- Bug tor-browser#42773: Replace ~ with the original HOME
- Bug tor-browser#43092: Disable Wayland by default in 14.0
- Bug tor-browser#43101: Security features warning links to Firefox installation support page with incomplete info
- Bug tor-browser#43141: Hardcode Arimo as a system-ui font
- Bug tor-browser#43196: Remove the vendor name from the "is playing media" notification on Linux
- Bug tor-browser-build#41237: Add some aliases to our Linux font config for compatibility
- Android
- Updated GeckoView to 128.3.0esr
- Bug tor-browser#41550: Remove unused extensions from Tor Browser for Android
- Bug tor-browser#42386: Remove unused assets to reduce APK size
- Bug tor-browser#42590: “Tor browser” text in top left of home fragment/new tab view gets cut off with larger text sizes
- Bug tor-browser#42655: Implement "New circuit for this site" on Android
- Bug tor-browser#42660: Review the patch on Android's ProxySelector
- Bug tor-browser#42731: Verify
privacy.spoof_englishstill works once we have Android builds - Bug tor-browser#42954: Remove product recommendation API integration (Review Mozilla 1857215)
- Bug tor-browser#43006: Disable RFP for Font Visibility on Android
- Bug tor-browser#43016: Re-disable Nimbus
- Bug tor-browser#43043: Remove credit card autofill UI elements from menu
- Bug tor-browser#43048: Firefox logo on splash
- Bug tor-browser#43050: Center text in connect buttons
- Bug tor-browser#43052: Remove non private tabs icon and "other device tabs" from tab view
- Bug tor-browser#43057: fenix/.../search/list.json failing linting
- Bug tor-browser#43078: Disable Sharing Links to TBA
- Bug tor-browser#43088: Query stripping is disabled on Android
- Bug tor-browser#43094: Remove "Open in regular tab" button
- Bug tor-browser#43097: NoScript fails to install on Android
- Bug tor-browser#43102: Android notifications tell to make Firefox your default browser
- Bug tor-browser#43108: Backport Android fullscreen notifications refactoring on ESR128
- Bug tor-browser#43114: Reader view uses the catch-all circuit on Android
- Bug tor-browser#43116: The lack of GeoIP databases produces a lot of spam in the console on Android
- Bug tor-browser#43128: Use DuckDuckGo HTML on the Safest security level for Android
- Bug tor-browser#43129: about:neterror cannot display SVG on Android with Security Level Safest
- Bug tor-browser#43132: Enable extensions installation on Tor Browser 14 for Android.
- Bug tor-browser#43146: Update the icon of DuckDuckGo onion search engine on Android
- Bug tor-browser#43147: Remove unused search plugins from the apk files
- Bug tor-browser#43151: MOZ_DATA_REPORTING, MOZ_TELEMETRY_REPORTING, MOZ_CRASHREPORTER, and MOZ_BACKGROUNDTASKS enabled on Android
- Bug tor-browser#43172: remove remote settings and SERPTelemetry
- Bug tor-browser#43202: Extensions page unnecessarily fetches recommended addons on Android
- Bug tor-browser#43223: Hide option to open bookmarks in non-private tabs on Android
- Bug tor-browser#43225: Hide non-private tab settings and history search on Android
- Bug tor-browser#43227: Hide the Firefox Suggest label above search suggestions on Android
- Bug tor-browser#43228: Fix the "What's new" URL and text on Android
- Bug tor-browser-build#41223: Tor Browser Alpha version not displayed correctly
- Build System
- All Platforms
- Updated Go to 1.22.8
- Bug tor-browser#42722: clang-format and localization linters are not running
- Bug tor-browser#42799: Do not run lint pipelines on new tag
- Bug tor-browser#43014: Add purgecaches to the dev build
- Bug tor-browser#43156: Update translation CI to account for the extended 13.5 release
- Bug tor-browser#43157: Move tb-dev to base-browser
- Bug tor-browser#43181: Run translation CI if there is a change in a string.xml file
- Bug tor-browser-build#41013: Add a README to each project
- Bug tor-browser-build#41096: Set SOURCE_DATE_EPOCH in the default env variables
- Bug tor-browser-build#41155: Update toolchains for ESR128
- Bug tor-browser-build#41156: Split the Rust configuration options
- Bug tor-browser-build#41180: Some files do not need to be copied when building tor-expert-bundle
- Bug tor-browser-build#41188: Upgrade binutils to 2.41
- Bug tor-browser-build#41189: Add matzfan to list of downstream projects in alpha release-prep template
- Bug tor-browser-build#41195: Update Go to 1.22
- Bug tor-browser-build#41198: Update release-prep issue template to include notifiying anti-censorship team of package name changes for GetTor distributor
- Bug tor-browser-build#41203: Tor Blog generation script uses the wrong url scheme for alpha releases
- Bug tor-browser-build#41236: Remove binutils when not needed
- Bug tor-browser-build#41273: relprep.py: bump Firefox and GV to a (yet) non-existing tag when the last one does not match HEAD
- Bug tor-browser-build#41274: Improve fetch_changelogs.py for major releases
- Bug tor-browser-bundle-testsuite#40078: Update tools/tb-build-06-start-nightly-build after tor-browser-build#40829
- Windows + macOS + Linux
- Bug tor-browser#42668: Drop torconnect rule in eslint-plugin-mozilla
- Bug tor-browser-build#41247: Adapt tools/update-responses/update_responses to support multiple versions in the same xml files
- Bug tor-browser-build#41256: tools/signing/upload-update_responses-to-staticiforme should regenerate update-responses when it already exists
- Bug tor-browser-build#41259: Don't try to generate incrementals for versions which don't set incremental_from
- Bug tor-browser-build#41270: Add updater rewriterules to make 13.5.7 a watershed
- Windows + macOS
- Bug tor-browser-build#41197: Modify update-responses to prevent upgrades on unsupported Windows and macOS versions
- Windows
- Bug tor-browser-build#29318: Drop mingw-w64/gcc toolchain
- Bug tor-browser-build#29320: Use mingw-w64/clang toolchain to build Rust
- Bug tor-browser-build#41185: Drop Windows 7 support for 14.0 from build tools
- Bug tor-browser-build#41201: Bump the Windows version checked by the installer
- macOS
- Bug tor-browser-build#41267: Go dropping support for macOS <= 11.0 in Go 1.23
- Android
- Bug tor-browser#42480: Use translation CI in android
- Bug tor-browser-build#40544: Bump Java 8 version to something more recent
- Bug tor-browser-build#41106: Non matching builds after application-services not being rebuilt in a long time
- Bug tor-browser-build#41123: Drop the firefox-android project
- Bug tor-browser-build#41171: Switch Android containers to Debian bookworm
- Bug tor-browser-build#41172: Refactor the android-toolchain project
- Bug tor-browser-build#41178: Force IPv4 when downloading in fix_gradle_deps.py
- Bug tor-browser-build#41200: Remove allowed_addons.json and the related tools
- Bug tor-browser-build#41210: Use tor-expert-bundle-aar in geckoview/build_apk
- Bug tor-browser-build#41211: The Android license file is not deterministic anymore
- Bug tor-browser-build#41214: Update geckoview/config to be more like firefox/config
- Bug tor-browser-build#41217: Update realprep.py script to handle Firefox 128-based Tor Browser Android
- Bug tor-browser-build#41224: Do not ship Conjure and GeoIP databases on Android x86, x86-64 to save some space
- Bug tor-browser-build#41232: Re-implement single-arch builds after the monorepo migration
- Bug tor-browser-build#41234: More dependencies are needed when building Android as a release
- Bug tor-browser-build#41261: Use an uncompressed NoScript xpi file to improve apk compression
- All Platforms
Comments
We encourage respectful, on-topic comments. Comments that violate our Code of Conduct will be deleted. Off-topic comments may be deleted at the discretion of the moderators. Please do not comment as a way to receive support or to report bugs on a post unrelated to a release. If you are looking for support, please see our FAQ, user support forum or ways to get in touch with us.